 Yesterday afternoon, I bundled up Chapter 4, Data Access with Spring Boot for Learning Spring Boot and shipped it off to Packt Publishing. They were happy to receive it on time.
Yesterday afternoon, I bundled up Chapter 4, Data Access with Spring Boot for Learning Spring Boot and shipped it off to Packt Publishing. They were happy to receive it on time.
Then I saw Spring Boot release version 1.1.5.RELEASE. I just updated all my source code to the latest version, edited the fragments, and fixed the links in my asciidoctor files. Reading through all the issues of this release, nothing appears to be of any impact to this book.
Naturally, I’ll recheck everything after I wrap up Chapter 5, Securing Your App. In the next and final chapter, I’ll show how Spring Boot speeds up securing apps. By merely adding Spring Security to your classpath, Spring Boot leaps into action and locks things down with suitable defaults. You can easily alter various settings. Finally, you can start plugging in custom configurations as needed.
 Security, in my experience, has historically been a tricky subject. I’ve seen countless teams apply security as the last step. People also don’t understand that security is a multi-layer effort. It’s not ALL contained in the application.
Security, in my experience, has historically been a tricky subject. I’ve seen countless teams apply security as the last step. People also don’t understand that security is a multi-layer effort. It’s not ALL contained in the application.
And security requires a certain understanding; a frame of mind. When I worked on the commercial engineering team a couple years ago, I applied several strategies to prevent users having their data compromises. Not all of these ideas were my own. Many came from a teammate that had a prankster’s perspective.
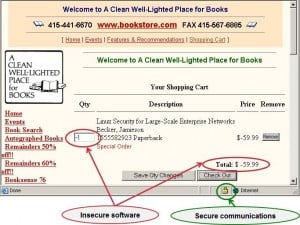
If you look at the second image in this blog, you’ll see a perfect depiction about how people will do something like configure SSL for a website and call it a day. SSL only secures one aspect of things. Usernames and passwords only cover a few more aspects.
This chapter will help cover how Spring Boot makes it much simpler to secure the embedded Tomcat servlet container. It will show how to institute authentication and authorization to verify you are who you say you are and that you’re authorized to do what you must. It’s important to plug in security from the get go, and Spring Boot makes this even easier than ever. But never stop looking for attack vectors that you must block to avoid issues.
0 Comments